By now, you’ve heard concerning the newest frontier AI fashions which might be remarkably good at discovering vulnerabilities in code and creating potential exploits. So good, the truth is, that these fashions have been considerably restricted from common use in an try to present defenders time to seek out and repair vulnerabilities earlier than attackers discover and exploit them.
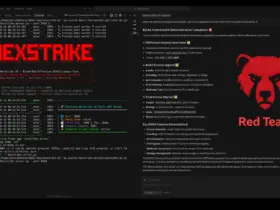
For context, on April 7, 2026, we started testing Anthropic’s Claude Mythos mannequin as a launch companion for Project Glasswing. Our conclusion was clear: The newest fashions are terribly succesful at discovering vulnerabilities and altering them into essential exploit paths in near-real-time. In Defender’s Guide to the Frontier AI Impact on Cybersecurity, I shared our early findings and suggestions.
Since then, we’ve continued testing the newest frontier AI fashions, together with Anthropic’s Mythos and Claude Opus 4.7 and OpenAI’s GPT-5.5-Cyber as a part of the Trusted Entry for Cyber program. The massive query just some weeks in the past was: “Are we overstating the mannequin capabilities?” With extra testing, I can confidently say we weren’t. In actual fact, these fashions are seemingly even higher at discovering vulnerabilities than we initially realized. At present, we’re offering an replace on our ongoing analysis, our learnings uncovered within the course of, and the method we’re taking to guard our prospects.
Discover and Repair Earlier than Attackers Discover and Exploit
At present, we launched our Could “Patch Wednesday” safety advisories, our month-to-month cadence of clear vulnerability disclosure and remediation. That is the primary time the place the vast majority of findings have been the results of frontier AI fashions scanning our code.
- These are the outcomes of the complete, preliminary scan of over 130 merchandise throughout all three platforms.
- As of in the present day, we’ve patched all necessary vulnerabilities in our SaaS delivered merchandise, and all customer-operated merchandise now have patches accessible.
- At present’s advisory covers 26 CVEs (representing 75 points) versus our traditional quantity (sometimes lower than 5 CVEs in a month); none of that are being exploited within the wild. Notice, this excludes CyberArk vulnerabilities, that are disclosed of their regular course of.
It is necessary to know this isn’t a one-and-done scenario. We’re now rescanning, making use of all our learnings about present the fitting context and risk intelligence to the fashions. We intend to repair each vulnerability we discover earlier than superior AI capabilities turn into extensively accessible to adversaries.
Whereas extremely highly effective, AI fashions aren’t merely magic. To attain high-fidelity outcomes, you might want to construct AI scanning harnesses, leverage context, guardrails and risk intelligence. We’ve additionally found a variance throughout fashions, as a result of variations of their coaching. A multimodel method is required to determine the superset of vulnerabilities. And at last, whereas the speedy precedence is discovering and fixing the vulnerabilities that organizations at present have, the longer-term shift is incorporating these fashions instantly into the software program growth lifecycle. That is the sunshine on the finish of the tunnel: A future the place software program is safe by design.
4 Steps Each Group Must Take Instantly
Whatever the present restricted entry, we imagine these capabilities will circulate extra broadly to different fashions. We now estimate a slim three-to-five-month window for organizations to outpace the adversary earlier than AI-driven exploits begin to turn into the brand new norm. This impending vulnerability deluge calls for urgency. Organizations that haven’t put acceptable safeguards in place will face a completely new class of threat. Right here’s what we advocate:
- Discover and Repair Vulnerabilities In Your Functions, Merchandise and Code
Discover and repair earlier than attackers discover and exploit.- Leverage AI fashions to determine vulnerabilities throughout all codebase.
- Apply the identical AI scanning to your open-source provide chain, and remediate or mitigate findings.
- Run accelerated patching tightly coordinated with product and growth groups.
- Assess, Cut back and Remediate Your Publicity
Cut back what’s reachable by attackers, safe what should be accessible, equivalent to customer-facing purposes.- Assault floor administration merchandise, like Cortex Xpanse®, have by no means been extra essential for locating and lowering publicity.
- The newest frontier AI fashions are very adept (with the fitting AI scanning harness) at evaluating exposures, understanding safety misconfigurations and prioritizing attack-path reachability.
- Audit your provide chain, together with AI infrastructure, runtime environments and mannequin dependencies.
- Guarantee Assault Protections
Vulnerability exploits are sometimes only one step of a multi-step assault lifecycle. Guaranteeing best-in-class protections is now much more necessary for stopping breaches.- Map present sensor protection to determine essential blind spots in detection, prevention and telemetry.
- Deploy best-in-class XDR in all places with an emphasis on real-time ML-based detection and prevention of assaults with all hosts on-premises and cloud included.
- Deploy Agentic Endpoint Safety to safe wide-scale adoption of vibe coding and AI safety throughout the enterprise (e.g. Prisma AIRS® and our current acquisition of Koi are actually a necessity for securing the agentic endpoint).
- Safe enterprise browsers with AI-based safety are a will need to have for securing the place customers now do their work.
- Zero belief and Id Safety are foundational to securing each person and connection, extending to inside segmentation and outbound utility connections.
- Deploy Actual-Time Safety Operations
Autonomous AI-driven assaults will drive assault lifecycles to minutes requiring each SOC to realize single-digit Imply Time To Detect (MTTD) and Imply Time To Reply (MTTR).- Assault detections should be AI/ML-driven to detect even regularly altering and novel assaults at scale.
- These AI detections should function towards a variety of first celebration and third celebration information sources. A greatest in school AI SOC should function on ALL related information sources.
- Automation, each natively built-in and all through the SOC lifecycle, is important to realize single-digit MTTR. This automation will more and more be agentic.
- This should be delivered as a platform to take away seams and gaps created by level options.
- Assess and act as shortly as potential.
Combating AI with AI — AI Frontier Safety Improvements Coming Quickly
Up to now, frontier AI fashions solely discover new assaults, not new assault methods. Which means with the fitting improvements, we are able to increase our use of AI to resolve the safety challenges that organizations are dealing with, and ship what our prospects want to remain forward of the ever-evolving risk panorama, together with:
- Reimagining digital patching with proactive, high-fidelity content material updates throughout community, endpoint and cloud safety – We anticipate that throughout open supply and expertise suppliers there shall be a deluge of patches, and digital patching will present a mitigation layer mandatory to present your groups time to replace. We anticipate to roll out the primary part of capabilities very quickly.
- Enhanced assault preventions, together with cyber-LLM skilled ML and small language fashions (SML) and habits protections – Early testing with Cortex XDR® and our community safety safety companies, equivalent to WildFire® malware prevention, point out excessive safety protection from the kinds of assaults created utilizing these new frontier AI fashions.
- Utilizing these fashions to scan our code, purposes and even safety configurations – Our intention is to productize these capabilities and incorporate them into our platforms.
Unit 42 — We’re Right here to Assist
We acknowledge that not everybody has the capability and/or experience to motion the entire suggestions to successfully counter frontier AI-driven dangers within the quick timeframe mandated by AI innovation. Our Unit 42 Frontier AI Defense service is designed to find and remediate your present publicity earlier than attackers do, strengthen controls that scale back publicity and include affect and modernize safety operations so groups can detect and reply at machine pace.
This can be a pivotal second for our trade. Whereas the dimensions of the problem introduced is actual, I’m assured in our potential to resolve it. We’re right here to assist our prospects navigate this transition and be certain that because the panorama continues to evolve, the benefit stays with the defender.
Ahead-Trying Statements
This weblog accommodates forward-looking statements that contain dangers, uncertainties and assumptions, together with, with out limitation, statements concerning the advantages, affect, or efficiency or potential advantages, affect or efficiency of our merchandise and applied sciences or future merchandise and applied sciences. These forward-looking statements are usually not ensures of future efficiency, and there are a major variety of elements that might trigger precise outcomes to vary materially from statements made on this weblog. We determine sure necessary dangers and uncertainties that might have an effect on our outcomes and efficiency in our most up-to-date Annual Report on Type 10-Ok, our most up-to-date Quarterly Report on Type 10-Q, and our different filings with the U.S. Securities and Change Fee from time-to-time, every of which can be found on our web site at buyers.paloaltonetworks.com and on the SEC’s web site at www.sec.gov. All forward-looking statements on this weblog are based mostly on info accessible to us as of the date hereof, and we don’t assume any obligation to replace the forward-looking statements supplied to replicate occasions that happen or circumstances that exist after the date on which they have been made.