Brokers have gone to work – on duties, sure, but additionally on code i.e. making requests inside reside manufacturing methods to invoke, join and make software calls in ways in which we might maybe not have envisaged half a decade in the past.
The truth signifies that builders as we speak want prolonged capabilities by way of runtime safety mannequin controls to supervise agent workflows.
Arcjet thinks it has the reply.
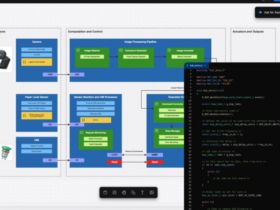
The corporate this week launched Guards, a service designed to implement safety inside AI agent workflows, queue customers (software code that queues for service requests, not folks in line on the grocery store – though in a roundabout approach, that too) and different software code that doesn’t run behind an HTTP request.
As extra software logic strikes into long-running agentic methods, the safety instruments constructed across the “request boundary” (by which we imply proxies, net software firewalls, HTTP middleware) can now not see the place untrusted enter arrives.
Guards prolong Arcjet’s runtime safety into these code paths.
Past single request simplicity

Arcjet CEO David Mytton: Safety has to reside the place the code lives.
Fashionable AI methods don’t run by way of a single request anymore. Brokers name instruments, pull in exterior information and “go state” throughout long-running workflows. Most of that execution by no means touches an HTTP boundary, which implies conventional safety controls by no means see it.
What all this implies is that builders apply guidelines instantly the place untrusted enter enters the applying, whether or not that enter comes from a software name, a queue message, or a workflow step.
That’s good, on the face of it, but it surely’s not ok.
Why…? As a result of, this motion places enforcement the place the applying’s actual context lives – identification, session state, prior software outputs, enterprise logic – slightly than at a community boundary that may’t see any of it.
“Safety has to reside the place the code lives. For agentic methods, meaning contained in the software calls and workflow steps the place untrusted enter truly arrives, not at a fringe that now not exists,” mentioned David Mytton, CEO at Arcjet. “Guards give builders a strategy to implement coverage contained in the code paths brokers use day by day – the identical place the menace mannequin now lives.”
Guards combine instantly into Arcjet’s application-layer safety mannequin. Builders outline guidelines in the identical codebase because the characteristic itself, so safety ships with the code and will get reviewed in the identical pull request. There isn’t any separate system to handle.
With Guards, groups can:
- Detect immediate injection in software outcomes earlier than they re-enter mannequin context.
- Block PII in software inputs and queue messages earlier than they attain third-party fashions.
- Implement per-user token budgets and spend limits inside agent loops.
- Validate untrusted enter in workflow steps, background jobs and different non-HTTP code paths.
- Guards work alongside current capabilities equivalent to Arcjet Defend for public endpoints, delicate information detection earlier than mannequin context is constructed and bot detection for high-cost AI routes. Collectively, these protections cowl each the boundary and the execution layer inside the applying.
Guards is obtainable now by way of the Arcjet JS and Python SDKs. Current prospects can allow it instantly; new builders can get began with a free trial.
 The Laptop Weekly Developer Community (CWDN) spoke to Mytton for extra.
The Laptop Weekly Developer Community (CWDN) spoke to Mytton for extra.
CWDN: How will Arcjet’s inside runtime mannequin particularly outperform conventional network-based WAFs when defending advanced, multi-step agentic software executions?
Mytton: The danger state of affairs is an agent escalating privilege throughout steps, draining a funds, or calling a software with arguments derived from untrusted context a number of hops again. That requires application-state consciousness – identification, session, route and the software name itself – which solely runtime enforcement inside the applying can see. The WAF was constructed for a world the place the HTTP request was the unit of intent. With brokers, the unit of intent is the software name, and that lives beneath the HTTP boundary.
CWDN: Since Guards combine instantly into code, how do you guarantee safety insurance policies stay constant throughout polyglot microservice environments?
Mytton: Generic insurance policies might be configured remotely by way of our cloud service after which utilized to each software request. Nonetheless, essentially the most highly effective and correct insurance policies all the time have to be near the code they’re defending – this is the reason it’s necessary for builders to take possession of safety identical to they’ve accountability for the database schema or observability.
CWDN: With logic transferring away from HTTP boundaries, what’s your long-term imaginative and prescient for the relevance of conventional perimeter safety?
Mytton: The perimeter nonetheless issues for issues the perimeter is sweet at: volumetric DDoS, geographic blocking, certificates termination. What’s modified is that an growing share of security-relevant selections can’t be made there anymore, as a result of the request hitting the perimeter now not represents the total intent. The perimeter isn’t going anyplace, however the runtime layer is the place the following decade of funding goes, as a result of that’s the place the brand new menace floor truly lives.
CWDN: Are you able to clarify how Guards successfully handle per-user token budgets when brokers function inside extremely unpredictable and recursive loops?
Mytton: Recursion is a non-issue from an enforcement standpoint – the SDK is invoked at each software name, so each leaf within the loop goes by way of the identical examine towards the identical per-user counter, no matter how deep the agent goes. Deciding what to do when a funds journeys mid-loop – fail the decision, degrade to a less expensive mannequin, or return the restrict again to the agent so it could actually replan – is a essential resolution. Guards surfaces these as specific coverage selections slightly than hiding them, as a result of the appropriate reply is dependent upon the applying.