AI coding instruments have moved from experiment to every day improvement help, serving to software program groups to draft features, clarify unfamiliar code, generate exams, and transfer by means of repetitive modifications sooner. For safety groups, the more durable query is how a lot AI-shaped code reaches a pull request earlier than anybody validates its security.
A latest Stack Overflow survey discovered that 46% of developers mistrust the accuracy of AI instrument output, whereas 33% belief it. That concern turns into seen throughout a routine safety evaluation. As an example, a generated API handler could compile and cross a unit take a look at whereas lacking object-level authorization. In the meantime, a urged dependency could look reputable whereas being deserted, susceptible, or suspiciously named.
The OWASP High 10 for Massive Language Mannequin Functions treats provide chain publicity as one of the major risks round LLM-enabled techniques. The checklist covers immediate injection, insecure output dealing with, delicate data disclosure, extreme company, and provide chain vulnerabilities. At present, these dangers are more and more permeating improvement environments, code assistants, pipeline automation, and AI-enabled functions.
How AppSec Platforms Are Adapting
AI-assisted improvement strains the older AppSec sequence of code evaluation, scan, ticket, and remediate. Extra code will be produced in much less time, and the identical insecure sample will be repeated throughout companies if a staff retains reusing a generated instance.
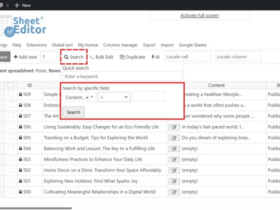
This underscores the necessity for an application security platform to attach findings throughout the event workflow, as a substitute of treating scanning as a separate checkpoint. A small AI-assisted change can contact a couple of layer: a brand new bundle, an API route, a config file, a container picture, or an infrastructure script would possibly all see the impression downstream.
The discovering solely turns into helpful when it’s tied to reachability, knowledge publicity, privilege degree, and the service affected. A vulnerability in a public API that touches buyer knowledge requires totally different dealing with from an identical flaw in unreachable take a look at code.
Probably the most helpful suggestions seems the place builders are already making selections, particularly inside pull requests, IDEs, and CI/CD checks. Reviewers may have to look at what modified, together with the assumptions the generated code carried into the mission.
Why Generated Code Modifications Evaluation
AI-generated code can look extra production-ready than it truly is. It’d use acquainted naming, frequent framework patterns, and polished construction. That polish can disguise weak authorization, unsafe defaults, or dependency decisions that reviewers could miss throughout a busy dash.
The issues often seem within the particulars. Generated code could also be too trusting of client-side enter, would possibly skip server-side authorization, expose detailed errors, over-log delicate knowledge, use outdated cryptographic examples, or counsel a bundle with out checking its upkeep historical past.
These are extraordinary AppSec failures, however AI instruments can produce them rapidly and in a type that seems prepared for manufacturing.
AI-generated fixes deserve the identical scrutiny as AI-generated options. A developer could ask an assistant to repair an injection danger and obtain a patch that addresses one parameter whereas leaving one other path uncovered. In authentication, fee, administrative, and customer-data workflows, generated fixes want the identical evaluation as generated options.
The place SDLC Controls Ought to Change
Governance ought to come first. Organizations ought to outline which AI coding instruments are accepted, what knowledge will be shared with them, and which repositories, information, or secrets and techniques are off limits. Builders ought to stay accountable for the code they commit, even when an assistant helped produce it.
Evaluation additionally wants a danger filter. A low-risk helper perform doesn’t want the identical evaluation path as code that touches identification, funds, buyer information, or administrative entry. Pull request templates can ask whether or not AI helped produce the change, whether or not new dependencies had been launched, and whether or not security-sensitive logic was modified.
Menace modeling ought to account for the place generated code enters the workflow, which assumptions it makes, and what an attacker might do if these assumptions fail. Safe software program improvement practices must be built-in into the SDLC fairly than dealt with as a remaining launch verify.
Controls That Cut back AI-assisted Code Threat
Dependency checks must catch AI-suggested packages earlier than they enter the mission. Builders mustn’t set up AI-suggested packages with out checking the supply, naming, upkeep, license, and recognized vulnerabilities. Typosquatting and bundle confusion are simpler to overlook when a urged library seems inside a quick coding move.
Secrets and techniques detection ought to run earlier than code reaches the principle department. Generated examples could embody placeholder keys, weak tokens, uncovered credentials, or unsafe configuration patterns. Blocking personal keys, API tokens, cloud credentials, and database secrets and techniques on the commit or pull request stage reduces avoidable publicity.
Authorization testing ought to show that the unsuitable consumer can not entry, change, or delete one other consumer’s knowledge. Public APIs and administrative features ought to embody horizontal and vertical privilege checks.
Enter and output validation must be reviewed in context. Generated code must be checked for injection dangers, unsafe deserialization, insecure file dealing with, improper encoding, and weak content-type controls. For AI-enabled functions, mannequin output must be handled as untrusted knowledge earlier than it reaches browsers, databases, shell instructions, plugins, or third-party companies.
If the identical AI-assisted sample retains producing lacking authorization checks, unsafe validation, or weak dependency decisions, the repair ought to transfer into safe templates, coding requirements, and extra particular developer steerage.
Prioritize Publicity, Not Quantity
When operating supply code safety checks, AI-assisted improvement can improve the variety of findings. Treating each alert with the identical urgency will sluggish groups down and weaken belief in safety tooling. Triage ought to start with what is definitely uncovered.
A medium-severity flaw in a public API dealing with buyer knowledge could require sooner motion than a essential concern in unreachable take a look at code. A susceptible bundle in a fee service carries a unique urgency from the identical bundle in an inner prototype. A helpful triage mannequin considers whether or not the susceptible path is reachable, internet-facing, tied to privileged actions, or related to delicate knowledge.
Builders additionally want findings that specify the affected path and the most secure repair. Generic warnings are simple to disregard beneath launch strain. A discovering is simpler to behave on when it factors to the affected path, explains the danger in that context, and suggests a repair that matches the framework getting used.
AppSec Must Maintain Tempo
AI coding instruments at the moment are a part of on a regular basis improvement, so safety applications must account for the way they modify code quantity, evaluation pace, and provenance. Generated code nonetheless wants possession, testing, and accountability. The groups that adapt finest would be the ones that transfer safety checks nearer to the purpose of creation, validate dependencies earlier than adoption, and prioritize the dangers more than likely to succeed in manufacturing.
(Photograph by Charlesdeluvio on Unsplash)