A malicious npm bundle named “tanstack” has been found deploying a stealthy information exfiltration marketing campaign, focusing on builders via a misleading naming technique and a hidden postinstall script.
The bundle, impersonating the well-known TanStack ecosystem, was weaponized to steal delicate atmosphere recordsdata instantly after set up.
The attacker registered the unscoped tanstack bundle title on npm, exploiting confusion with the official @tanstack group, which maintains extensively used libraries like TanStack Question and TanStack Desk.
By presenting the bundle as a “TanStack Participant” SDK with polished documentation and lifelike branding, the risk actor created a convincing entice for unsuspecting builders.
Assault Timeline and Conduct
On April 29, 2026, between 17:08 and 17:35 UTC, the attacker printed 4 speedy updates: variations 2.0.4 via 2.0.7. Every model contained a postinstall hook, a script that executes routinely throughout npm set up.
Earlier model 2.0.3, printed in March, confirmed no malicious conduct. The sudden introduction of the postinstall script marked the beginning of the assault.
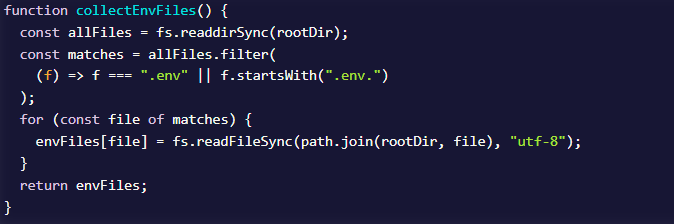
As soon as triggered, the script silently reads atmosphere recordsdata reminiscent of .env and .env.native from the developer’s system and sends their contents to an attacker-controlled endpoint.
The stolen information is shipped to a Svix webhook endpoint, a official webhooks-as-a-service platform. By routing exfiltration via a trusted supplier, the attacker reduces the possibility of detection by community safety instruments.
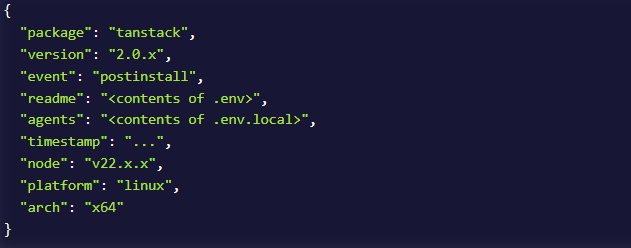
The payload contains:
- Surroundings file contents.
- System metadata reminiscent of Node.js model, OS, and structure.
- Bundle model and timestamp.
Apparently, the script disguises delicate information underneath deceptive discipline names like “readme” and “brokers,” masking the true nature of the exfiltrated content material.
The speedy launch cycle suggests the attacker was actively testing and refining the malware in actual time:
- 2.0.4: Preliminary focusing on of
.envrecordsdata, no opt-out mechanism. - 2.0.5: Momentary shift to innocent recordsdata (seemingly testing exfiltration pipeline).
- 2.0.6: Most harmful model, scanning all
.env.*variants together with manufacturing recordsdata. - 2.0.7: Reverts focusing on however provides uncommon self-dependency.
This sample signifies dwell debugging and optimization whereas the bundle remained publicly obtainable.
What Information Is at Threat
Surroundings recordsdata usually include extremely delicate credentials, together with:
- AWS entry keys.
- GitHub and npm tokens.
- Database connection strings.
- API keys for providers like Stripe, Twilio, and OpenAI.
- OAuth secrets and techniques and different personal configurations.
If a .env.manufacturing file was current, production-level secrets and techniques might have been uncovered.
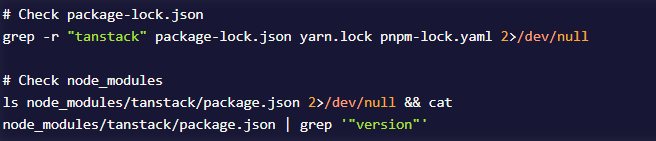
Builders ought to instantly verify for the presence of affected variations (2.0.4–2.0.7) in lock recordsdata or node_modules. If discovered, assume compromise and rotate all uncovered credentials.
Key response actions:
- Revoke and regenerate API keys and tokens.
- Overview cloud logs (e.g., AWS CloudTrail) for suspicious exercise.
- Audit CI/CD pipelines, as postinstall scripts execute throughout automated builds.
- Monitor outbound site visitors to
api.svix.comround set up time.
No persistence mechanisms had been recognized, however the information theft is everlasting as soon as executed.
This incident highlights ongoing dangers within the open-source ecosystem, notably title squatting assaults. A easy typo putting in tanstack as a substitute of @tanstack/question may end up in full credential publicity.
To cut back threat:
- Confirm bundle scope and writer earlier than set up
- Use lockfile integrity checks and dependency scanning instruments
- Contemplate safe bundle managers or instruments that block recognized malicious packages
This marketing campaign underscores how rapidly attackers can weaponize belief in standard ecosystems, turning a routine set up command right into a silent information breach.
Observe us on Google News, LinkedIn, and X to Get Immediate Updates and Set GBH as a Most popular Supply in Google.