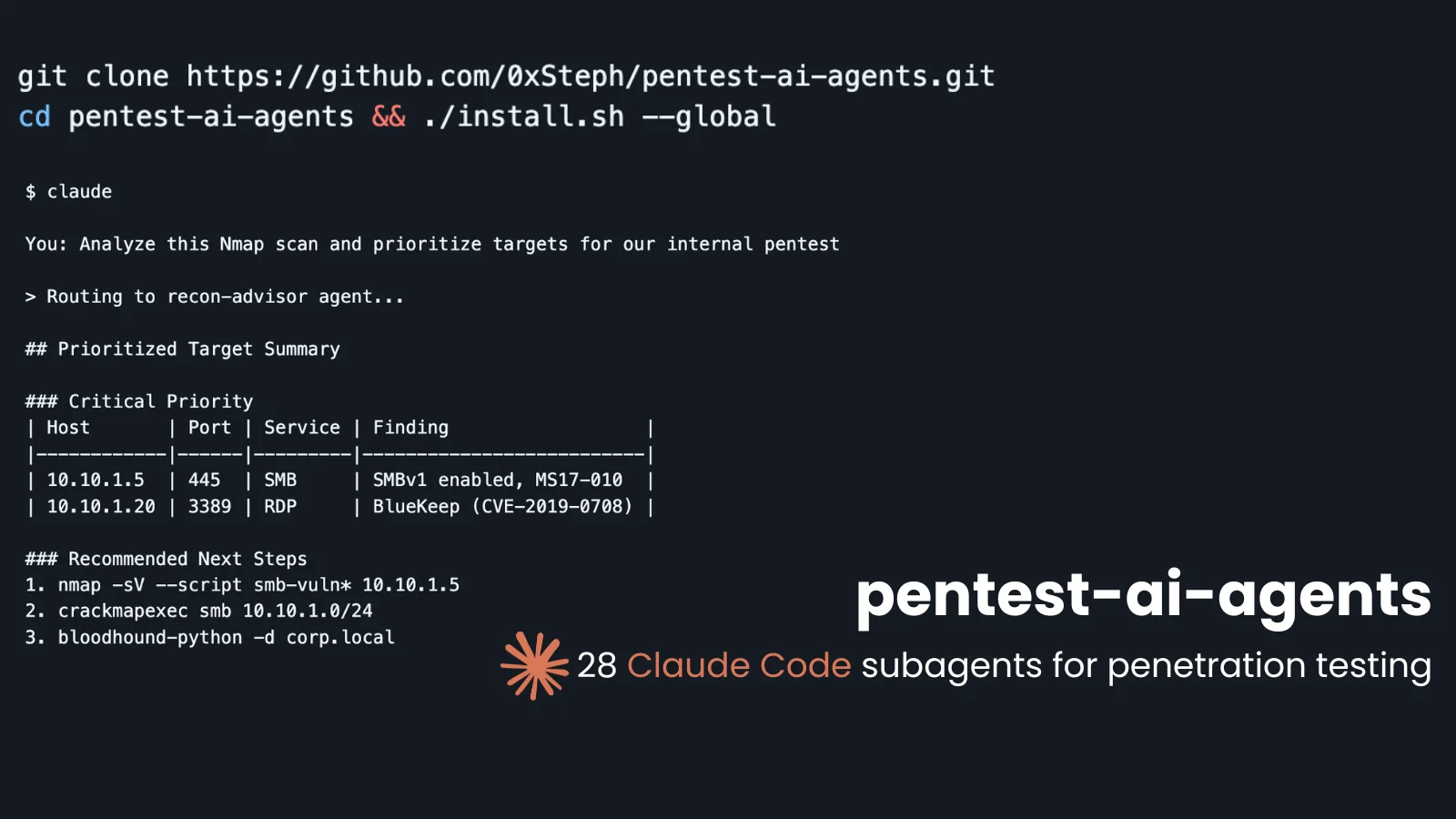
A brand new open-source toolkit known as pentest-ai-agents is redefining how safety professionals leverage AI in penetration testing workflows, remodeling Anthropic’s Claude Code into a totally specialised offensive safety analysis assistant powered by 28 domain-specific subagents.
Launched by safety researcher 0xSteph on GitHub, pentest-ai-agents is a group of 28 Claude Code subagents, every carrying deep area experience throughout the complete penetration testing lifecycle.
Protection spans reconnaissance, internet utility testing, Energetic Listing assaults, cloud safety, cellular pentesting, wi-fi assaults, social engineering, exploit chaining, detection engineering, forensics, malware evaluation, and report era.
Reasonably than counting on a single general-purpose AI mannequin, the framework routinely routes every question to essentially the most applicable specialist agent.
Pentest-AI-Brokers Set up
Setup requires no servers, no exterior dependencies, and no complicated configuration. A single command handles all the pieces:
bashcurl -fsSL https://uncooked.githubusercontent.com/0xSteph/pentest-ai-agents/important/set up.sh | bash
The script clones the repository, copies all 28 agent recordsdata to ~/.claude/brokers/, and exits cleanly. It’s absolutely idempotent, which means re-running it safely updates present brokers.
Further set up choices assist project-scoped deployments (--project) and a cost-optimized lite mode (--global --lite) that runs advisory brokers on Claude Haiku for diminished token consumption.
The toolkit introduces a two-tier execution mannequin for security and suppleness. Tier 1 brokers function in advisory mode, customers paste device output, and obtain prioritized evaluation, methodology steerage, and beneficial subsequent instructions.
Tier 2 brokers go additional, composing and executing instructions immediately towards a declared, licensed scope, with Claude Code displaying every command for specific approval earlier than execution.
Tier 2 brokers embrace the Recon Advisor (nmap, whois, whatweb), Internet Hunter (ffuf, sqlmap, dalfox), AD Attacker (BloodHound, Impacket, CrackMapExec, Certipy), Exploit Chainer, PoC Validator, and Enterprise Logic Hunter. Each offensive motion is mapped to MITRE ATT&CK identifiers and paired with defensive context.
Persistent Findings and MCP Assist
A built-in SQLite-backed findings database (findings.sh) persists engagement information throughout Claude Code periods, enabling multi-day operations with seamless handoffs.
Tier 2 brokers write to this database routinely when findings.sh is within the system PATH. The Report Generator agent produces skilled pentest stories full with government summaries, CVSS scoring, and remediation roadmaps.
For air-gapped or privacy-sensitive environments, brokers will be transformed to OpenCode customized instructions suitable with Ollama, LM Studio, or any native mannequin by way of the included opencode-setup.sh script.
A companion MCP server (pentest-ai) extends the ecosystem with 150+ device wrappers, autonomous exploit chaining, and CI/CD pipeline integration for Claude Desktop, Cursor, and VS Code Copilot.
Observe us on Google News, LinkedIn, and X for every day cybersecurity updates. Contact us to function your tales.